CLOUD OR EDGE IN THE AGE OF AI?
As fast as cloud computing and cloud-based AI has
centralized processing, IoT devices create a better
and more automated security net. IHS Markit fore-
casts 125 billion such devices by 2030. According
to Accenture’s 2018 Technology Vision Report, “To
fully enable real-time intelligence, businesses must shift
event-driven analysis and decision processing closer
to points of interaction and data generation. Delivering
intelligence in the physical world means moving closer
to the edge of networks.”
Moving AI technology to the edge may be leveraged
for a variety of security and safety applications moving
forward; however, thermal management of the microprocessor
has been the limiting factor. The new breed
of AI chipsets runs complex AI algorithms
more efficiently.
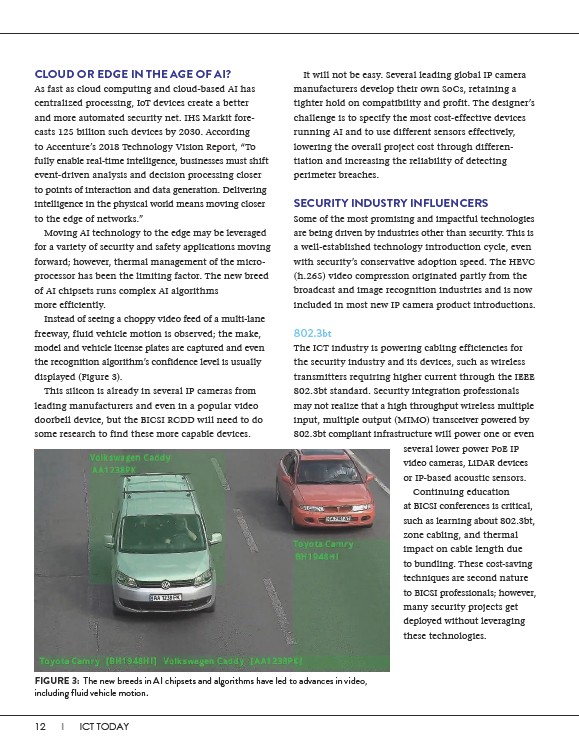
Instead of seeing a choppy video feed of a multi-lane
freeway, fluid vehicle motion is observed; the make,
model and vehicle license plates are captured and even
the recognition algorithm’s confidence level is usually
displayed (Figure 3).
This silicon is already in several IP cameras from
leading manufacturers and even in a popular video
doorbell device, but the BICSI RCDD will need to do
some research to find these more capable devices.
12 I ICT TODAY
It will not be easy. Several leading global IP camera
manufacturers develop their own SoCs, retaining a
tighter hold on compatibility and profit. The designer’s
challenge is to specify the most cost-effective devices
running AI and to use different sensors effectively,
lowering the overall project cost through differentiation
and increasing the reliability of detecting
perimeter breaches.
SECURITY INDUSTRY INFLUENCERS
Some of the most promising and impactful technologies
are being driven by industries other than security. This is
a well-established technology introduction cycle, even
with security’s conservative adoption speed. The HEVC
(h.265) video compression originated partly from the
broadcast and image recognition industries and is now
included in most new IP camera product introductions.
802.3bt
The ICT industry is powering cabling efficiencies for
the security industry and its devices, such as wireless
transmitters requiring higher current through the IEEE
802.3bt standard. Security integration professionals
may not realize that a high throughput wireless multiple
input, multiple output (MIMO) transceiver powered by
802.3bt compliant infrastructure will power one or even
FIGURE 3: The new breeds in AI chipsets and algorithms have led to advances in video,
including fluid vehicle motion.
several lower power PoE IP
video cameras, LiDAR devices
or IP-based acoustic sensors.
Continuing education
at BICSI conferences is critical,
such as learning about 802.3bt,
zone cabling, and thermal
impact on cable length due
to bundling. These cost-saving
techniques are second nature
to BICSI professionals; however,
many security projects get
deployed without leveraging
these technologies.