When BAS devices are
not configured properly,
important data
collection suffers.
July/August 2019 I 45
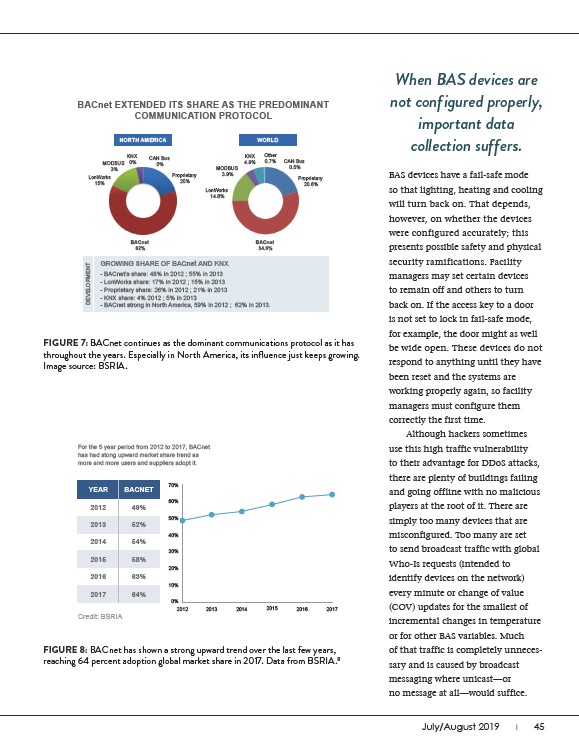
BACnet EXTENDED ITS SHARE AS THE PREDOMINANT
COMMUNICATION PROTOCOL
NORTH AMERICA WORLD
MODBUS
3%
KNX
0%
CAN Bus
0%
Proprietary
20%
BACnet
62%
MODBUS
3.9%
KNX
4.9%
Other
0.7% CAN Bus
0.5%
Proprietary
20.6%
LonWorks
14.8%
BACnet
54.6%
LonWorks
15%
GROWING SHARE OF BACnet AND KNX
- BACnet’s share: 48% in 2012 ; 55% in 2013
- LonWorks share: 17% in 2012 ; 15% in 2013
- Proprietary share: 26% in 2012 ; 21% in 2013
- KNX share: 4% 2012 ; 5% in 2013
- BACnet strong in North America, 59% in 2012 ; 62% in 2013.
DEVELOPMENT
FIGURE 7: BACnet continues as the dominant communications protocol as it has
throughout the years. Especially in North America, its influence just keeps growing.
Image source: BSRIA.
For the 5 year period from 2012 to 2017, BACnet
has had stong upward market share trend as
more and more users and suppliers adopt it.
YEAR
BACNET
2012 49%
70%
60%
50%
40%
30%
20%
10%
0%
2012
2013 52%
2014 54%
2015 58%
2016 63%
2017 64%
Credit: BSRIA
2013 2014 2015 2016 2017
FIGURE 8: BACnet has shown a strong upward trend over the last few years,
reaching 64 percent adoption global market share in 2017. Data from BSRIA.8
BAS devices have a fail-safe mode
so that lighting, heating and cooling
will turn back on. That depends,
however, on whether the devices
were configured accurately; this
presents possible safety and physical
security ramifications. Facility
managers may set certain devices
to remain off and others to turn
back on. If the access key to a door
is not set to lock in fail-safe mode,
for example, the door might as well
be wide open. These devices do not
respond to anything until they have
been reset and the systems are
working properly again, so facility
managers must configure them
correctly the first time.
Although hackers sometimes
use this high traffic vulnerability
to their advantage for DDoS attacks,
there are plenty of buildings failing
and going offline with no malicious
players at the root of it. There are
simply too many devices that are
misconfigured. Too many are set
to send broadcast traffic with global
Who-Is requests (intended to
identify devices on the network)
every minute or change of value
(COV) updates for the smallest of
incremental changes in temperature
or for other BAS variables. Much
of that traffic is completely unnecessary
and is caused by broadcast
messaging where unicast—or
no message at all—would suffice.